Shake'Up, Wavestone's startup accelerator, is pleased to present the first edition of the “Women Entrepreneurs in Tech” prize. Conceived and piloted jointly with the French newspaper Les Echos, this prize will be awarded on March 5, 2025. The aim is…
The Digital Operational Resilience Act (DORA) is a European regulation designed to enhance the resilience of financial entities against IT and cybersecurity risks. Its ambitious objective is to improve organizations’ ability to anticipate and manage crises while optimizing their operational…
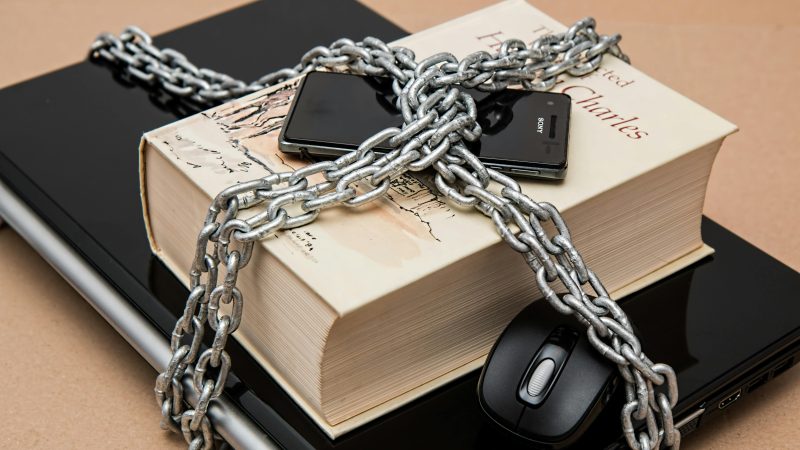
Managing access rights to an organisation's resources is a central issue in IAM. An authorisation model provides a layer of abstraction that guides the allocation of technical permissions to users and makes it easier to monitor them over time. To…
With the European Union’s ban on the sale of combustion engine vehicles set for 2035, the electric mobility market is rapidly expanding. Alongside it, electric vehicle charging infrastructures (EVCI) are developing at a fast pace: cumulative investments by 2030 could…
The massive deployment of artificial intelligence solutions, with complex operation and relying on large volumes of data in companies, poses unique risks to the protection of personal data. More than ever, it appears necessary for companies to review their tools…
Brief introduction to mainframe Mainframe computers play a central role in the daily operations of the world’s largest corporations. It dominates the landscape of large-scale business computing in banking, finance, health care, insurance, public utilities, government, and a multitude of…
Since the boom of Large Language Models (LLMs) and surge of AI use cases in organisations, understanding how to protect your AI systems and applications is key to maintaining the security of your ecosystem and optimising the use for the…
Artificial intelligence (AI) is transforming numerous sectors, including the industrial sector. The latest advancements, particularly those based on Machine Learning (ML) like generative AI, are paving the way for new opportunities in process automation, supply chain optimization, personalization, and so…
The online payments market is constantly changing: to illustrate, from 2022 to 2023, the number of mobile payments has increased by 90.4%, and for e-money payments, the increase was 29.7%[1]. In order to manage this evolution, the European Union has…
Microsoft has announced that in Q2 2024 "more than half of Fortune 500 companies will be using Azure OpenAI". [1] At the same time, AWS is offering Bedrock [2], a direct competitor to Azure OpenAI. This type of platform can…