IEC 62351 is an international cybersecurity standard for Smart Grid communication and control systems. Its aim is to help grid operators protect themselves against threats endangering this sector, while adapting the recommendations to the realities of the industrial world. In…
Category: Formats
On March 13, 2024, the European Parliament adopted the final version of the European Artificial Intelligence Act, also known as the “AI Act”[1]. Nearly three years after the publication of the first version of the text, the twenty-seven countries of…
Chief Identity Officer (CIdO). That's the new term introduced by Gartner to define the role of an identity manager within an organization. While this term is still relatively new, upcoming challenges regarding digital identity could well elevate the CIdO to…
Recent advances in artificial intelligence (AI) promise a revolution in every aspect of our lives, both professional and personal. This transformation is affecting every job within our companies, raising questions about the impact of AI in well-established areas such as…
The use of artificial intelligence systems and Large Language Models (LLMs) has exploded since 2023. Businesses, cybercriminals and individuals alike are beginning to use them regularly. However, like any new technology, AI is not without risks. To illustrate these, we…
Since its initial appearance in 2014 and following its formalization in 2021 under the auspices of the Biden administration, the concept of SBOM (Software Bill of Materials) continues to captivate attention within the cyber community. CISOs, CIOs and DevSecOps teams…
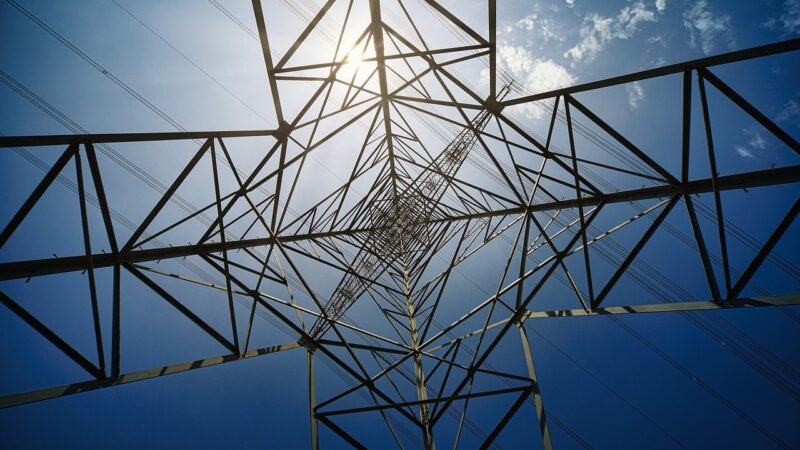
Introduction Industrial systems are a category of information systems of their own, with codes and properties that differ from "classic" IT systems. It is well known that the level of maturity of the industrial sector in terms of cybersecurity is…
About the study: This study is based on publicly available data up to Q3 2023 and aims to outline the various active Vulnerability Disclosure initiatives within the 100 largest banks and the EU countries. Bug Bounty? A Bug Bounty program…
Today, cyber-attacks are part of our daily lives, and are becoming increasingly common and sophisticated. Simultaneously, we are moving towards Information Systems that are built on an ever-increasing diversity of environments, thanks in particular to the Cloud, which is now…
Data and collaborative spaces migration to the cloud has created new data breach possibilities and has particularly extended the attack surface of companies. Furthermore, cloud applications increasing utilization and new ways of working have considerably widened - whether voluntary or…