Generative AI systems are fallible: in March 2025, a ChatGPT vulnerability was widely exploited to trap its users; a few months earlier, Microsoft's health chatbot exposed sensitive data; in December, a simple prompt injection allowed the takeover of a user…
Will AI also revolutionize cybersecurity? Today, there's every reason to believe so! After a decade of massive investment in cybersecurity, we are a period of consolidation. Optimization is becoming the watchword: automate repetitive tasks, rationalize resources, detect ever faster and…
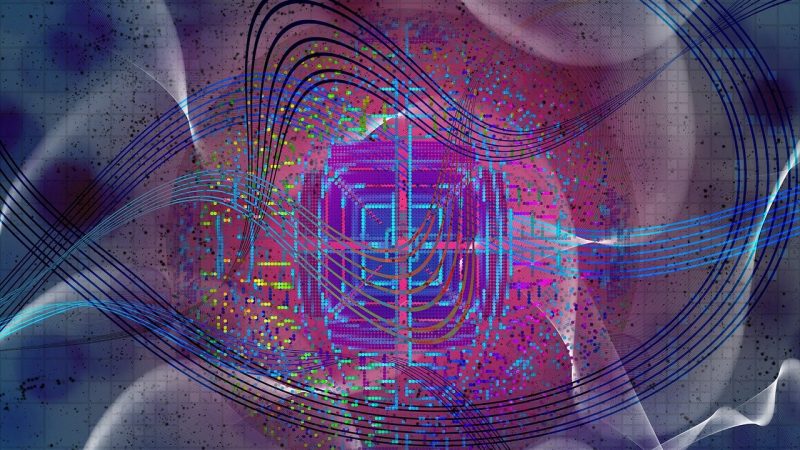
What if your most sensitive data became accessible in an instant? The growing excitement about the advent of quantum computers is justified for a subject that is no longer science fiction but involves a new kind of threat. Indeed, according…
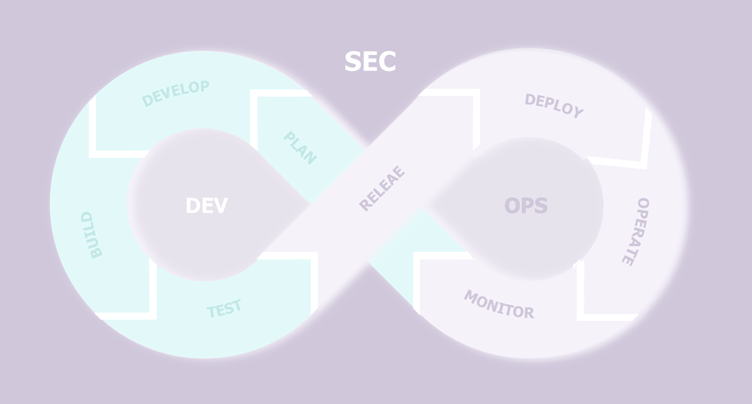
Over the past few years, companies have been rapidly adopting security tools to protect their applications across the development lifecycle, leveraging DevSecOps scanners such as SAST, DAST, SCA, and scanners for containers, Infrastructure-as-Code, and secrets. Progressively, the goal has shifted…
According to the 2024 Verizon report, the human factors is responsible for 68% of data breaches. Aware of this vulnerability, 90% of cyberattacks exploit human error, with phishing as the primary attack vector. In this context, it has become essential…
In the first article of this series, we explored the foundation of Microsoft’s Enterprise Access Model (EAM), focusing on the critical task of scoping the Control Plane to safeguard cloud administration. We delved into the evolving security landscape, where the…
This article is the first of a series of 2, tackling the implementation of the Enterprise Access Model, an administration model proposed by Microsoft to secure the administration of Cloud environments. Today, most companies use public cloud to host…
Quantum computing threatens today’s asymmetric cryptography and would render current algorithms obsolete, both RSA and ECC. As for symmetric cryptography, (AES, hash functions) doubling the key size ensures maintained security guarantees. To address the threat, the NIST has standardized three…
In a world where aviation safety is increasingly based on digital systems, the PART-IS regulation introduced by the European Union Aviation Safety Agency (EASA) marks a decisive turning point. This innovation is due to increasing numbers of cybersecurity standards, regulations,…
Shake'Up, Wavestone's startup accelerator, is pleased to present the first edition of the “Women Entrepreneurs in Tech” prize. Conceived and piloted jointly with the French newspaper Les Echos, this prize will be awarded on March 5, 2025. The aim is…
With the European Union’s ban on the sale of combustion engine vehicles set for 2035, the electric mobility market is rapidly expanding. Alongside it, electric vehicle charging infrastructures (EVCI) are developing at a fast pace: cumulative investments by 2030 could…
The massive deployment of artificial intelligence solutions, with complex operation and relying on large volumes of data in companies, poses unique risks to the protection of personal data. More than ever, it appears necessary for companies to review their tools…
Brief introduction to mainframe Mainframe computers play a central role in the daily operations of the world’s largest corporations. It dominates the landscape of large-scale business computing in banking, finance, health care, insurance, public utilities, government, and a multitude of…
Since the boom of Large Language Models (LLMs) and surge of AI use cases in organisations, understanding how to protect your AI systems and applications is key to maintaining the security of your ecosystem and optimising the use for the…
Artificial intelligence (AI) is transforming numerous sectors, including the industrial sector. The latest advancements, particularly those based on Machine Learning (ML) like generative AI, are paving the way for new opportunities in process automation, supply chain optimization, personalization, and so…
The online payments market is constantly changing: to illustrate, from 2022 to 2023, the number of mobile payments has increased by 90.4%, and for e-money payments, the increase was 29.7%[1]. In order to manage this evolution, the European Union has…
Microsoft has announced that in Q2 2024 "more than half of Fortune 500 companies will be using Azure OpenAI". [1] At the same time, AWS is offering Bedrock [2], a direct competitor to Azure OpenAI. This type of platform can…
For the last few weeks, I have been developing a full custom Command and Control (C2). This C2 uses several Windows DLL for network communication and specially the WINHTTP.DLL one to handle HTTP requests used for the HTTP and HTTPS…
Artificial intelligence (AI) now occupies a central place in the products and services offered by businesses and public services, largely thanks to the rise of generative AI. To support this growth and encourage the adoption of AI, it has been…
Enterprise demand for detection probes has been rising in recent years, particularly in the industrial sector. This can be for many reasons: regulatory or contractual constraints, need for incident detection capabilities on the industrial network, desire for greater visibility on…
Large Language Models (LLMs) such as GPT-4 have revolutionized Natural Language Processing (NLP) by achieving unprecedented levels of performance. Their performance relies on a high dependency of various data: model training data, over-training data and/or Retrieval-Augmented Generation (RAG) enrichment data.…
Since the Covid crisis, we've seen an increase in the frequency of cyberattacks on the industrial sector. Between 2019 and 2020, the number of such attacks has quadrupled, taking the form of ransomware in 80% of the cases[1], and potentially…
Ever since the launch of ChatGPT in November 2022, many companies began developing and releasing their own Large Language Models (LLMs). So much so that we are currently in a phase that many experts describe as an “AI Race”. Not…
This summer's post-quantum news: what you need to know This summer marks a major breakthrough in cybersecurity with the publication of the NIST standards for post-quantum cryptography. This publication is the culmination of many years of work, the standardisation process…
The banking sector has rapidly modernized, and online banking has become a matter of course for both banks and their customers. These players are increasingly reliant on the Internet, with all the advantages that implies, but also the risks. At…
1. Overview In an information system, applications are not equal. Some of them can be used as an entry point in the information system, others are used as compromise accelerators, and some are saved for post-exploitation. These applications are called…
Not familiar with CMMC 2.0? For more information regarding CMMC 2.0, please refer to this article. The Cybersecurity Maturity Model Certification (CMMC) is a comprehensive framework designed to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI), shared with…
Identity & Access Management (IAM) is an "old" topic for companies. Virtually all major groups have already carried out several IAM projects, often with the growing aim of pooling, centralizing and standardizing. And while those involved in these projects are…
Historically, Switzerland has distinguished itself from its neighbors by adopting a less stringent approach to information system security regulations. Preference has been given to subsidiarity, a legal principle whereby the Confederation does not legislate in areas where the Cantons can.…
Here we are, on May 21, 2024, the European regulations on AI see the light of day after 4 years of negotiations. Since February 2020, the European Union (EU) has been interested in Artificial Intelligence Systems (AIS) with the publication…
The need for a regal digital identity stems from the need to guarantee the reliability of online exchanges and transactions, in the face of rising fraud in a context of increasing dematerialization. The European Union responded by introducing the eIDAS…
Step 0: context and objectives Wavegame is a Wavestone inter-school challenge designed to promote cybersecurity expertise and the consulting profession created in 2019. In its 2023 edition, 33 teams competed in a hands-on exercise focused on securing an AWS Infrastructure.…
Among the technologies that seemed like science fiction only a few decades ago and are now an integral part of the digital ecosystem, Facial Recognition (FR) holds a prominent place. Indeed, this tool is increasingly present in our daily lives:…
This article is intended primarily for an informed public, mastering the use of cryptographic keys in an IS and their management in organizations. Increasing security requirements for both industrial environments and connected objects have led to a profusion of cryptographic…
The IAM market has considerably matured as it relates to its coverage of classic "employee" use cases and is increasingly focusing on the "customer" perimeter- both on the part of IAM solution vendors and the companies deploying them. Over the…
In the age of hybrid information systems, securing cloud resources is a cornerstone of enterprise security. Faced with constantly evolving threats and increasingly complex IT environments, companies are seeking more effective and scalable cloud information systems and access management solutions. …
In late October 2023, a third-party data breach incident sent shockwaves through the business world, affecting over 57,000 entities engaged in business with Bank of America. This breach exposed sensitive personal and financial information, underscoring the pivotal role that third-party…
On March 13, 2024, the European Parliament adopted the final version of the European Artificial Intelligence Act, also known as the “AI Act”[1]. Nearly three years after the publication of the first version of the text, the twenty-seven countries of…
Chief Identity Officer (CIdO). That's the new term introduced by Gartner to define the role of an identity manager within an organization. While this term is still relatively new, upcoming challenges regarding digital identity could well elevate the CIdO to…
Recent advances in artificial intelligence (AI) promise a revolution in every aspect of our lives, both professional and personal. This transformation is affecting every job within our companies, raising questions about the impact of AI in well-established areas such as…
The use of artificial intelligence systems and Large Language Models (LLMs) has exploded since 2023. Businesses, cybercriminals and individuals alike are beginning to use them regularly. However, like any new technology, AI is not without risks. To illustrate these, we…
Introduction Industrial systems are a category of information systems of their own, with codes and properties that differ from "classic" IT systems. It is well known that the level of maturity of the industrial sector in terms of cybersecurity is…
About the study: This study is based on publicly available data up to Q3 2023 and aims to outline the various active Vulnerability Disclosure initiatives within the 100 largest banks and the EU countries. Bug Bounty? A Bug Bounty program…
Today, cyber-attacks are part of our daily lives, and are becoming increasingly common and sophisticated. Simultaneously, we are moving towards Information Systems that are built on an ever-increasing diversity of environments, thanks in particular to the Cloud, which is now…
Data and collaborative spaces migration to the cloud has created new data breach possibilities and has particularly extended the attack surface of companies. Furthermore, cloud applications increasing utilization and new ways of working have considerably widened - whether voluntary or…
Today, cyber-attacks are part of our daily lives, and are becoming increasingly numerous and sophisticated. Simultaneously, we are moving towards Information Systems built on an ever-increasing diversity of environments, thanks in particular to the Cloud, which is now…
During the Wavestone OT Cyber Day, Loïc Lebain and Benoit Bouffard conducted a workshop in which they noted that IT departments were still struggling to develop a catalogue of cybersecurity solutions for OT. Based on their experience with our customers,…
Containers represent an opportunity for rapid, flexible, and efficient application deployment. In 2019, 84% of production infrastructures were already using containers[1]. As it is often the case, this massive adoption has taken place without the integration of Cybersecurity teams, sometimes…
Securing privileged access through access management is vital because it ensures that an organisation’s people are only granted access to what they need to do their jobs, and only for the period for which they need it. Access management also allows…
“Talent shortage”, “skills gap”, “employee burnout in cybersecurity”, “high turnover rate” – as a cybersecurity professional, you must be familiar with these expressions, for better or for worse. You may have seen the big headlines pointing out talent shortage issues…
The PIPL (Personal Information Protection Law) has emerged as an unprecedented first example of highly protective regulation of personal data, establishing an uncertain framework that reinforces China's control. Despite recent clarifications from China’s authorities, the centralisation of information systems continues…
China may soon ease PIPL cross-border data transfer requirements, but your privacy compliance strategy should focus on the long term. Your company operates in China. You compile personal data relating to your Chinese employees and transfer them to your headquarters…
The industrial control system (ICS) is the set of resources and machines used to supervise and control an industrial process. This article looks at the security issues surrounding Windows devices of the ICS supervision and maintenance layer: SCADA servers and…
Confidential and strategic, the due diligence phase that precedes an acquisition regularly takes place behind closed doors. This phase aims to analyse the target company for an acquisition, in order to determine its level of maturity and compliance on various…
The dawn of generative Artificial Intelligence (GenAI) in the corporate sphere signals a turning point in the digital narrative. It is exemplified by pioneering tools like OpenAI’s ChatGPT (which found its way into Bing as “Bing Chat, leveraging the GPT-4…
Integrating security directly into the configuration of CI/CD pipelines, especially through the practice of DevSecOps, enables the development of secure applications while increasing delivery frequency. This relieves pressure on security teams, which can often be a limiting factor in the…
On a daily basis, stakeholders within construction handle a variety of data that may be of interest to malicious parties. They are subjected to the same types of malware attacks as players in other industries (e.g. theft, espionage, phishing, etc.).…
Back in 2021, a video of Tom Cruise making a coin disappear went viral. It was one of the first deepfake videos, videos that both amused and frightened Internet users. Over the years, artificial intelligence in all its forms has…
While studying internals of a mechanism used by all EDR software to get information about processes activities on Windows, we came across a way for malicious processes to disable the generation of some security events related to process interactions. This…
As you know, artificial intelligence is already revolutionising many aspects of our lives: it translates our texts, makes document searches easier, and is even capable of training us. The added value is undeniable, and it's no surprise that individuals and…
Process injection is a family of malware development techniques allowing an attacker to execute a malicious payload into legitimate addressable memory space of a legitimate process. These techniques are interesting because the malicious payload is executed by a legitimate process…
Cyber Month is to cybersecurity awareness what the Olympics are to sports: the time to shine, with all eyes on you. Given that human-risk remains significant, with human error accounting for 82% of data breaches according to the 2022 Verizon…
A 38% increase of cyber-attacks was estimated in 2022[1]. As this figure illustrates, the cyber threat continues to grow, and has become a major concern for businesses worldwide. To counter this growing threat and maintain digital confidence, governments have long…
Intro The emergence of the Industry 4.0 is characterized by the digitization of industry and greater interconnection between the various machines that make up an industrial IS (Information System). However, this growth in communications within industrial Control Systems also…
In November 2022, the conversational agent ChatGPT developed by OpenAI was made accessible to the general public. Since then, it's an understatement to say that this new tool has garnered interest. Just two months after its launch, the tool became…
At the end of June 2017, an image shocked the minds of the cyber security and business continuity world. An open space, filled with workstations, all displaying the same screen: the NotPetya ransomware message. Even today, 90% of the…
Most organisations are still insufficiently prepared for a possible compromise of their Information System, leading to its destruction. Taking this risk into account right from the project design stage will enable them to significantly strengthen their resilience capabilities. On…
In 2023, Artificial Intelligence has received unprecedented media coverage. Why? ChatGPT, a generative artificial intelligence capable of answering questions with astonishing precision. The potential uses are numerous and go beyond current comprehension. So much so that some members of the…
Introduction The ever-increasing threat of cyber-attacks on organisations around the world and their potentially devastating financial, reputational, or operational impact on the business means it has never been more important to position Cyber Security as a major issue in front…
Active Directory is a critical asset whose failure affects a large portion of your information system Your company is currently dealing with a major ransomware crisis. Given its central role in managing access, authentication, and network resources within any organisation,…
For over twenty years, Wavestone has been supporting clients develop and strengthen their Identity and Access Management programs. Within this area, Wavestone has observed that organizations do not always approach IAM in a comprehensive manner. While Security is an obvious…
Introduction Definition of electronic voting Electronic voting is a dematerialised, self-counting voting system in which voters use electronic devices to record their votes. The system can be used remotely via internet voting, or in person where voters can visit polling…
Here are the topics of this newsletter edition: A well-known bot often used for cyber-attacks, the Qakbot The First responder Word FOCUS TECH QAKBOT Initially designed to steal banking credentials, Qakbot has evolved into a more versatile malware with multiple…
Hello Roxane! Thank you for your time! Today, we’re going to talk about the Operational Resilience Maturity Assessment Framework. Could you summarize the tool in one sentence? To sum up, the Operational Resilience Maturity Assessment Framework is a tool that…
Internet of Things (IoT) platforms enable the connection, management and monitoring of fleets of devices. The 3 cloud leaders, GCP, AWS and Azure each have their own offering, in a particularly fragmented sector, which sees many players competing. Azure, in…
A quick overview of phishing techniques on Azure and Office 365 Phishing attacks are well known. The objective of this type of attack is to perform actions from a victim's account or to retrieve information about the targeted person or…
An overview of the different cybercriminal uses case of ChatGPT The one year report about the cyber operations between Ukraine and Russia, by the CERT-EU CHATGPT What opportunities for the underground world of cybercrime ? Need a refresh about…
The increasing maturity of technologies associated with the use of digital certificates The use of digital certificates on information systems has been around for over 20 years. It is a proven practice based on standardised technologies and regulations governing several…
M365 is a true catalyst for collaborative work, having to respond to the increase in internal threats that result. The importance of the M365 suite in business The Microsoft 365 software suite offers a critical set of collaborative services for…
DORA, in a nutshell The European Union published the Digital Operational Resilience Act, or “DORA”, on December 27th, 2022, and it entered into force on January 16th, 2023. It sets new rules for financial entities and their ICT third-party service providers…
The ISO 27001 and ISO 27002 standards provide a set of requirements and best practices to organize and implement an Information Security Management System (ISMS) within any organization. The success of these standards has been widely observed both in France…
In nearly 90% of the incidents managed by Wavestone CERT [1], the Active Directory domain was compromised: rapid rebuilding capabilities are no longer an option. However, the backup and recovery of Active Directory environments is a subject that has long…
Preparing for crisis management is now necessary for most companies and large organizations. Conscious of the risk or driven by regulations (the DORA regulation is a good example), crisis exercises and simulations have become an unmissable annual event. Even if…
How to ensure the security of your applications despite outsourcing their development? Integrating security into projects is an important process for companies to define and integrate security aspects into products as early as possible. This avoids increasing the cost…
Who would have known that locking your employees in a room for 15 minutes could become their new favorite way to learn about cybersecurity? In a never-ending quest to find innovative ways to raise awareness on cybersecurity topics, the Wavestone team…
Regularly rethinking your cyber strategy is a must for cybersecurity teams. Changes in the threat, regulations, business priorities, etc., necessitate an in-depth review of the action plan at least once every three years, or yearly, if necessary. To accomplish this,…
Once again, the CERT-W 2022 report confirms that the main motivation of attackers continues to be financial gain and ransomware remains the most common means of extortion. Ransomware attacks are among the most severe cyberattacks in terms of their impact on…
Dashboards are an essential tool for CISOs to measure and control risks in their scope, to steer their projects and to inform their management of the company’s cyber health evolution. However, according to Wavestone’s Cyber benchmark results from 2022, 47%…
Introduced just over 10 years ago by Forrester, Zero Trust is a security philosophy that starts from the premise that the cyber threat is omnipresent, both outside and inside the IS, and consequently proposes an access management strategy based on…
During protests in Philadelphia towards the end of May 2020, two police vehicles were set on fire. Photos of the event posted on Instagram and cross-referencing of aliases, visible on Etsy, Poshmark and LinkedIn, will lead[1] an FBI investigator to…
The increase in cyberattacks witnessed over the last few years can be partially attributed to the evolution and spread of automation tools, which are leveraged to perform wider attacks with fewer resources. Many steps of an attack can be automated…
If you work in cybersecurity, you have probably heard of the OWASP TOP 10: a standard awareness document that represents a broad consensus about the most critical security risks to web applications. However, in Industrial Control Systems, we never talk…
In recent years, organisations have undertaken major projects to secure their Active Directory (AD). These projects have been launched to counter the threat of a massive compromise of the AD system in order to deploy ransomware, of which there are…
This year again, we were delighted to be able to share our knowledge during Hacker Summer camp (cybersecurity conferences that happen roughly at the same time in Las Vegas each year: BlackHat, BSides Las Vegas, and DEFCON). (Thomas is…
Feedback on AWS and Azure Misconfigurations in cloud environments are still a source of major incidents and will keep on reoccurring endlessly. With the news continuously providing new examples: leakage of 1 billion citizens' data linked to a key leak,…
Is it necessary to engage in DevSecOps because projects work in Agile? A few questions need to be asked to get a clearer picture. In previous articles, we talked a lot about how security should be organised to accompany agile…
For the third consecutive time, the French city of Toulon hosted the French southernmost hacking event known as Barb'hack. We - two of Wavestone security auditors - have had the opportunity to attend the conference and participate in the Capture-the-Flag (CTF) event…
Today, many companies have initiated a migration to the public cloud, and this brings its share of benefits, but also new attack surfaces. In this article, we will look at how companies can best manage their security posture, by verifying…
The use of "guest" identities to facilitate collaboration externally The need for collaboration externally entails risks for companies Companies have always needed to collaborate with each other by sharing resources and exchanging data. To do this, their collaborators must…
The content of this article is taken from an interview conducted by Marc JACOB for Global Security Mag in March 2022, available here. The obviousness of IAM, and the difficulty of the transformations it implies Faced with the…
We recently learned from AdvIntel researcher Yelisey Boguslavskiy that the Russian group Conti shut down its operation, thereby making the brand obsolete.[1] This announcement comes only a few months after it was the center of attention of the specialized press…
This article was originally published on our corporate website wavestone.com on 26 January 2023. Cybersecurity awareness is a journey to embed secure behaviours in people's daily lives To do so, you need to build a strong cyberawareness program, focus…
































































![[INTERVIEW] IAM Maturity Assessment – Where do you stand and why is it crucial?](https://www.riskinsight-wavestone.com/wp-content/uploads/2023/01/Image1-800x450.jpg)